SSH - Secure Shell is a cryptographic network protocol used for secure connection between a client and a server. The protocol supports various authentication mechanisms. The two most popular mechanisms are passwords based authentication and public key based authentication.
Before generating a new SSH key pair, first check if you already have an SSH key on your client machine so you don’t overwrite your existing keys.
To check for existing SSH keys:
If there are existing keys, you can either use those and skip the next step or backup up the old keys and generate a new one.
If you do not see such file or directory it means that you do not have an SSH key and you can proceed with the next step and generate a new one.
The following command will generate a new 4096 bits SSH key pair with your email address as a comment:
Press Enter to accept the default file location and file name:
Next, the ssh-keygen tool will ask you to type a secure passphrase. Whether you want to use passphrase it’s up to you, if you choose to use passphrase you will get an extra layer of security.
If you don’t want a passphrase press Enter.
The entire process looks like this:
username@hostname:~/.ssh$ ssh-keygen -t rsa -b 4096 -C "watson.josh@particlerobots.com"
Generating public/private rsa key pair.
Enter file in which to save the key (/home/username/.ssh/id_rsa):
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /home/username/.ssh/id_rsa
Your public key has been saved in /home/username/.ssh/id_rsa.pub
The key fingerprint is:
SHA256:00KUT9Ln7eo9LDiTTcSuSgSdqfC7XlTduojc+txt4aQ watson.josh@particlerobots.com
The key's randomart image is:
+---[RSA 4096]----+
| .o |
| oooo... |
| . . =+.+... |
| o + o. +.. |
| o S .o.. |
| = = .o.+ |
| . = o*.* . |
| + o*.Eo= |
| .o ooo+ooo. |
+----[SHA256]-----+
username@hostname:~/.ssh$
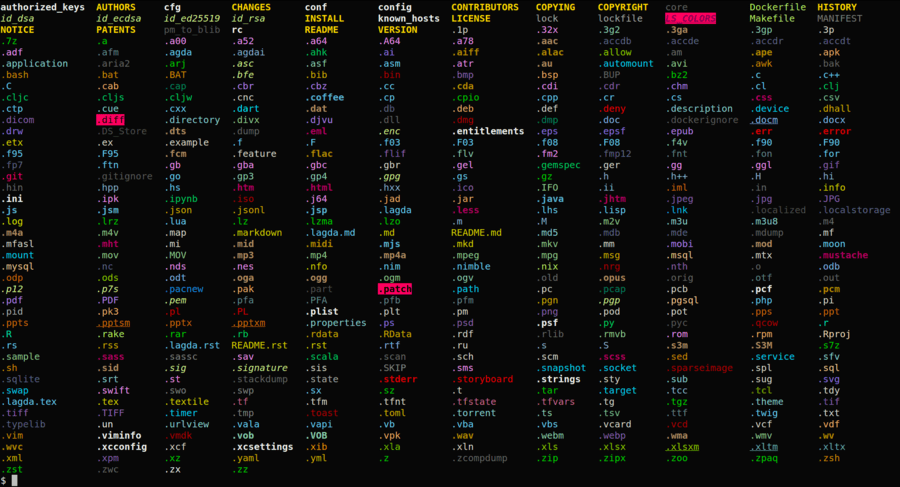
To make sure that the SSH key is generated:
ls ~/.ssh/id_* /home/username/.ssh/id_rsa /home/username/.ssh/id_rsa.pub
Now that you have generated an SSH key pair, in order to be able to login to your server without a password you need to copy the public key to the server you want to manage.
The easiest way to copy your public key to your server is to use a command called ssh-copy-id. On your local machine terminal type:
You will be prompted to enter the remote_username password:
Once the user is authenticated, the public key will be appended to the remote user authorized_keys file and connection will be closed.
username@hostname:~/.ssh$ ssh-copy-id watsonjosh@10.25.120.215 /usr/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed /usr/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys watsonjosh@10.25.120.215's password: Number of key(s) added: 1 Now try logging into the machine, with: "ssh 'watsonjosh@10.25.120.215'" and check to make sure that only the key(s) you wanted were added. username@hostname:~/.ssh$ ssh watsonjosh@10.25.210.215
If by some reason the ssh-copy-id utility is not available on your local computer you can use the following command to copy the public key:
After completing the steps above you should be able log in to the remote server without being prompted for a password.
To test it just try to login to your server via SSH:
If everything went well, you will be logged in immediately.
username@hostname:~/.ssh$ ssh 'watsonjosh@10.25.120.215' Welcome to Ubuntu 18.04.5 LTS (GNU/Linux 4.9.140-tegra aarch64) * Documentation: https://help.ubuntu.com * Management: https://landscape.canonical.com * Support: https://ubuntu.com/advantage This system has been minimized by removing packages and content that are not required on a system that users do not log into. To restore this content, you can run the 'unminimize' command. 262 updates can be applied immediately. 61 of these updates are standard security updates. To see these additional updates run: apt list --upgradable Last login: Tue Nov 2 14:18:49 2021 from 10.25.120.150 watsonjosh@watsonjosh-nx:~$